












Why privileged access demands absolute control
Privileged accounts can reset security controls, alter infrastructure, create identities, grant permissions, and disable monitoring. In hybrid environments, that authority often extends further than expected.
Unmanaged, it becomes a critical vulnerability.
Privileged Access Management (PAM) governs how elevated access is approved, time‑limited, monitored, and removed. It reduces standing privilege and closes the gaps attackers exploit, including risks introduced by non‑human identities and emerging agentic AI workflows.
At Kocho, we design Privileged Access Management that that keeps powerful access under control and aligned to real business risk.
Why privileged access risk grows without you noticing
Privilege rarely expands deliberately. It accumulates through operational convenience, architectural inconsistency, and decisions that made sense at the time.
Persistent standing access
Elevated roles remain assigned beyond operational necessity, increasing exposure with every account that outlives its purpose.
Fragmented hybrid governance
Cloud and on-premises admin identities follow different governance patterns, creating blind spots that are difficult to audit and easy to exploit.
Informal elevation workflows
Access requests handled by email or manual approval leave no structured audit trail, making it impossible to verify who approved what and when.
Unmanaged service and workload privilege
Application, automation and AI agent identities accumulate excessive permissions over time, rarely reviewed and rarely removed.
Effective PAM governs identity and access as a single discipline
Privileged Identity Management (PIM) governs who holds elevated roles. Privileged Access Management governs what those roles allow and how access is exercised. In modern hybrid environments, these disciplines must operate together.
Organisations are not simply managing roles or tools.
They’re governing the privileged user as the core unit of control across cloud and on-premises systems.
Kocho designs integrated privileged access architectures that connect identity lifecycle, elevation control, credential governance, and monitoring into a unified operating model, eliminating the fragmentation and structural gaps that attackers exploit.
Why we govern privileged access as a lifecycle, not an event
Effective PAM extends beyond just-in-time activation. Every privileged identity, whether human, service account or AI Agent, must be governed from creation to removal, with nothing left to operational assumption.
Kocho designs PAM solutions that govern the full privileged identity lifecycle:
- How administrative accounts are created and structured
- How elevation is requested, approved, and time-bound
- How credentials are controlled and rotated
- How activity is monitored and evaluated
- How access is removed when it is no longer required
The result is privileged access that is aligned to identity governance, responsive to workforce change, and defensible at every stage.
There were a lot of unmanaged accounts in the system. We needed a way to automate the provisioning and de-provisioning of accounts, to streamline the process, and prevent security breaches.
Principal IT Officer
Stafford University
Why hybrid environments make privileged access harder to govern
Cloud and on-premises administrative identities rarely evolve under the same governance model. Over time that inconsistency compounds, and the gaps it creates becomes an exploitable attack surface.
Without a unified approach, organisations face:
- Inconsistent elevation controls across cloud and on-premises environments
- Divergent credential handling practices that are difficult to audit
- Service accounts that outlive operational need and accumulate excessive permissions
- Limited visibility across hybrid infrastructure that weakens threat detection
A mature privileged access strategy must rationalise control models across the entire estate. At Kocho, we align hybrid privileged access into a cohesive framework that enforces least privilege consistently, whether access originates in the cloud or on-premises.
Privileged access is where Zero Trust matters most
Nowhere is the principle of Zero Trust more critical to enforce than across your privileged identities, where the consequences of misplaced trust are greatest.
Structured privileged access management is central to any credible Zero Trust architecture:
- Eliminating unnecessary standing privilege across cloud and on-premises environments
- Enforcing time-bound elevation so access exists only when it is needed
- Requiring strong authentication for every high-risk role activation
- Applying contextual evaluation before elevation is granted
- Monitoring privileged activity in near real-time to detect anomalous behaviour
- Ensuring structured deprovisioning so access does not outlive its purpose
- Ensuring the same principles apply equally to AI agents, automations, and service identities
The result is privilege that is dynamic, visible, and risk-aware. Least privilege stops being a principle and becomes an operating reality.
How mature organisations govern privileged access end to end
Effective PAM is not a single control. It is a set of disciplines that work together to govern every stage of the privileged user journey.
Identity lifecycle governance
Privileged accounts must be created, structured, and removed through automated, auditable workflows. Manual provisioning creates gaps that accumulate into serious risk over time.
Just-in-time elevation
Standing privilege is the enemy of least privilege. Elevation should be time-bound, approval-based, and automatically revoked when the operational need has passed.
Credential management
Passwords and secrets associated with privileged accounts must be rotated automatically, stored securely, and never left to manual handling or individual memory.
Contextual access control
Elevation should never be unconditional. Strong authentication, risk-based evaluation, and contextual signals must be applied before any high-privilege role is activated.
Continuous monitoring
Privileged activity must be logged, evaluated, and acted upon in near real-time. Suspicious behaviour should trigger immediate response, not a retrospective audit finding.
Structured deprovisioning
Access that is not actively removed is access that persists. Privileged accounts must be automatically disabled or removed when roles change, projects end, or people leave.
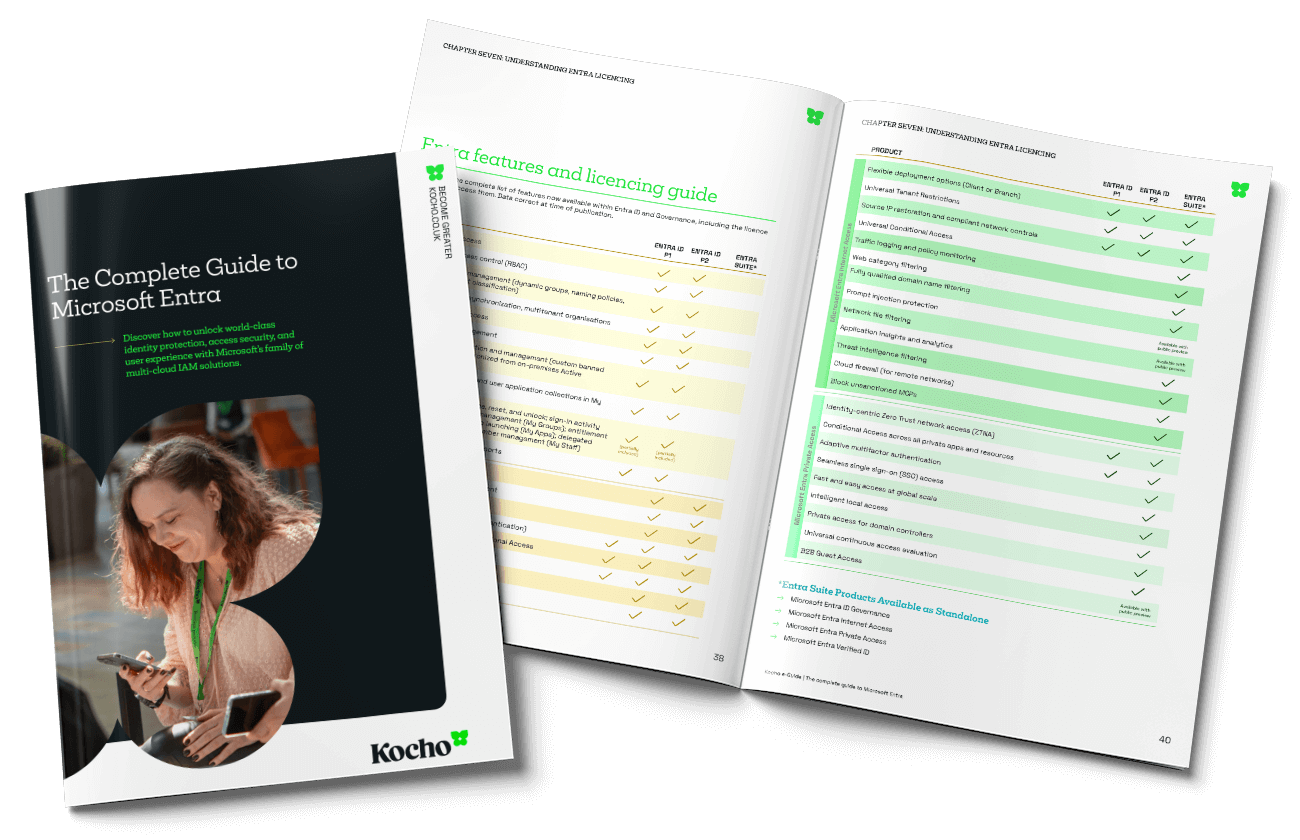
Why we build PAM solutions on Microsoft Entra
Microsoft Entra is a Forrester and Gartner market leader for PAM solutions.
Privileged Identity Management, role-based access control, Conditional Access, identity risk signals, and hybrid administrative integration combine to support the full privileged user lifecycle across cloud and on-premises environments. The capability is there. The question is knowing how to unlock it.
As a Microsoft partner and global leader in identity solutions we bring the architectural expertise to turn that capability into a structured, enterprise-grade operating model.
We design privileged access frameworks that are aligned to your governance requirements, compliance obligations, and Zero Trust strategy, built on technology your organisation already owns or has within reach.

Case studies
Who we've helped
Ready to review your privileged access controls?
When privileged access drifts, risk grows quietly in the background.
Talk to our identity specialists about bringing privileged access back under clear, consistent control.
Frequently asked questions about privileged access management (PAM)
-
Privileged access management governs how elevated permissions are assigned, activated, monitored, and removed across an organisation. It reduces standing privilege, enforces structured control over high-risk administrative access, and ensures that the accounts with the greatest authority are the most tightly governed.
-
Privileged accounts can reset security controls, alter infrastructure, create identities, and disable monitoring. Unmanaged, they represent the most significant vulnerability in any enterprise environment. PAM reduces that exposure by ensuring elevated access is only available when it is needed, to whom it is needed, and for as long as it is needed.
-
Privileged Identity Management governs who holds elevated roles and how those roles are assigned and reviewed. Privileged Access Management governs what those identities can do, controlling elevation, credentials, authentication, and monitoring. In modern hybrid environments both disciplines must work together as a unified model.
-
By limiting the duration of elevated permissions, just-in-time access reduces the window of exposure if credentials are compromised. It enforces least privilege by ensuring administrative access exists only when there is an active operational need.
-
Yes. A mature privileged access strategy must align cloud administrative roles and on-premises directory accounts under a unified governance and enforcement model. Inconsistent controls across hybrid estates are one of the most common sources of exploitable privilege gaps.
-
Zero Trust assumes breach and eliminates implicit trust. PAM enforces that principle where it matters most, applying dynamic, risk-aware controls over the most sensitive roles in the environment and ensuring elevation is never unconditional.
-
Standing privilege refers to elevated access that remains permanently assigned rather than activated only when needed. It increases exposure because compromised credentials immediately grant high-level access without any additional verification or approval.
-
When architected correctly, Microsoft Entra and Azure-native capabilities support core PAM requirements across identity lifecycle, just-in-time elevation, credential governance, and monitoring across cloud and on-premises environments. For a detailed technical walkthrough of how these components integrate, read our in-depth guide to privileged user management in Microsoft Entra.
-
Privileged access maturity can be assessed across several dimensions including the extent of standing privilege, consistency of elevation controls across hybrid environments, credential rotation practices, audit coverage, and alignment to identity governance and Zero Trust principles.
-
Any organisation operating hybrid infrastructure, scaling cloud adoption, or operating under regulatory compliance obligations should treat PAM as a foundational security control. The risk of unmanaged privilege grows in proportion to the complexity of the environment.
-
Agentic AI often operates through non-human identities (service principals, workload identities, API tokens) to perform tasks across systems. PAM ensures those identities are time-bound where possible, tightly scoped to least privilege, strongly authenticated, and fully audited so autonomous actions remain governed and defensible.

























Don't Miss
Great identity governance resources


A clear pathway
Book your Entra ID Discovery & Roadmapping Workshop
Understand how to achieve more efficient, secure, and cost-effective identity and access management.
This is your opportunity to:
- Understand the gaps and challenges costing your organisation time and money.
- Gain a strategy that aligns identity management with your long-term business goals.
- Design an affordable solution that mitigates security risks and improves user experiences.