Everything starts with identity and access management






















When identity and access management is strong, greatness follows
Identity and access management (IAM) is the foundation of every security, compliance, and operational decision. It defines who has access, under what conditions, and with what level of confidence.
As attackers target credentials and AI, automation, and SaaS demand faster, broader access, identity has become the primary attack surface. Accumulated technical debt, including legacy directories, fragmented models, and inconsistent controls, magnifies the risk.
Securing identity requires more than tools. It demands a coherent identity and access management (IAM) strategy that reduces complexity, controls access at scale, and supports modern Microsoft‑based architectures.
Kocho helps organisations deliver IAM programmes built for today’s threats and long‑term change.
Where identity risk and operational drag take hold
In complex environments, identity is where security breaks down and operational overhead accumulates.
Legacy platforms compound technical debt
Platforms built for a previous era create integration friction and growing technical debt that becomes harder to resolve over time.
Fragmented identity sources
Multiple directories and disconnected provisioning tools create inconsistency, producing unreliable access control and audit exposure.
Cloud adoption exposes architecture
On-premises identity models weren’t designed for hybrid environments. As cloud adoption accelerates, the architectural gap widens into structural risk.
Ungoverned application access creates gaps
Legacy and SaaS applications rarely share a common identity standard. Without unified control, entitlements sprawl and oversight breaks down.
IAM built by design, not default
Identity estates rarely start clean. They usually accumulate over time through mergers, legacy platforms, SaaS adoption, and tactical security decisions.
Common characteristics include fragmented directories, inconsistent authentication standards, manual access processes, standing privilege, and limited visibility into who has access to what. Even where modern platforms like Microsoft Entra are in place, identity capabilities are often deployed in isolation rather than as part of a coherent architecture.
This fragmentation creates security gaps attackers can exploit, while making it difficult for organisations to scale access securely across cloud services, partners, and emerging AI workloads.
When identity architecture no longer fits modern needs
Identity challenges arise when architecture becomes fragmented or weighed down by technical debt and no longer reflects how the organisation operates.
Common constraints include:
- Legacy MIM deployments with years of custom logic
- Pre‑API integrations and hard‑to‑maintain scripts
- Application‑specific identity silos
- Static or manual access models that limit consistency
These constraints increase overhead, create governance gaps, and limit flexibility at scale.
Modern IAM replaces fragmentation with a unified, cloud‑aligned architecture built on Microsoft Entra, guided by Kocho through structured, low‑risk phases.
A structured approach to identity and access management
Kocho treats identity and access management as a clear, structured roadmap.
Each discipline tackles a specific part of the identity estate and is introduced in phases that reflect real-world maturity, risk, and how the organisation operates.
Together, these disciplines create a strong Zero Trust identity foundation that supports steady progress, balancing security improvement with day‑to‑day operational stability.
The thing that stands out about Kocho is their level of professionalism and the experience they have in identity and access management. They are market leaders and that really shows.
Stuart Perkiss-Webb
Infrastructure Architect, Aviva
One identity platform, built on Microsoft Entra
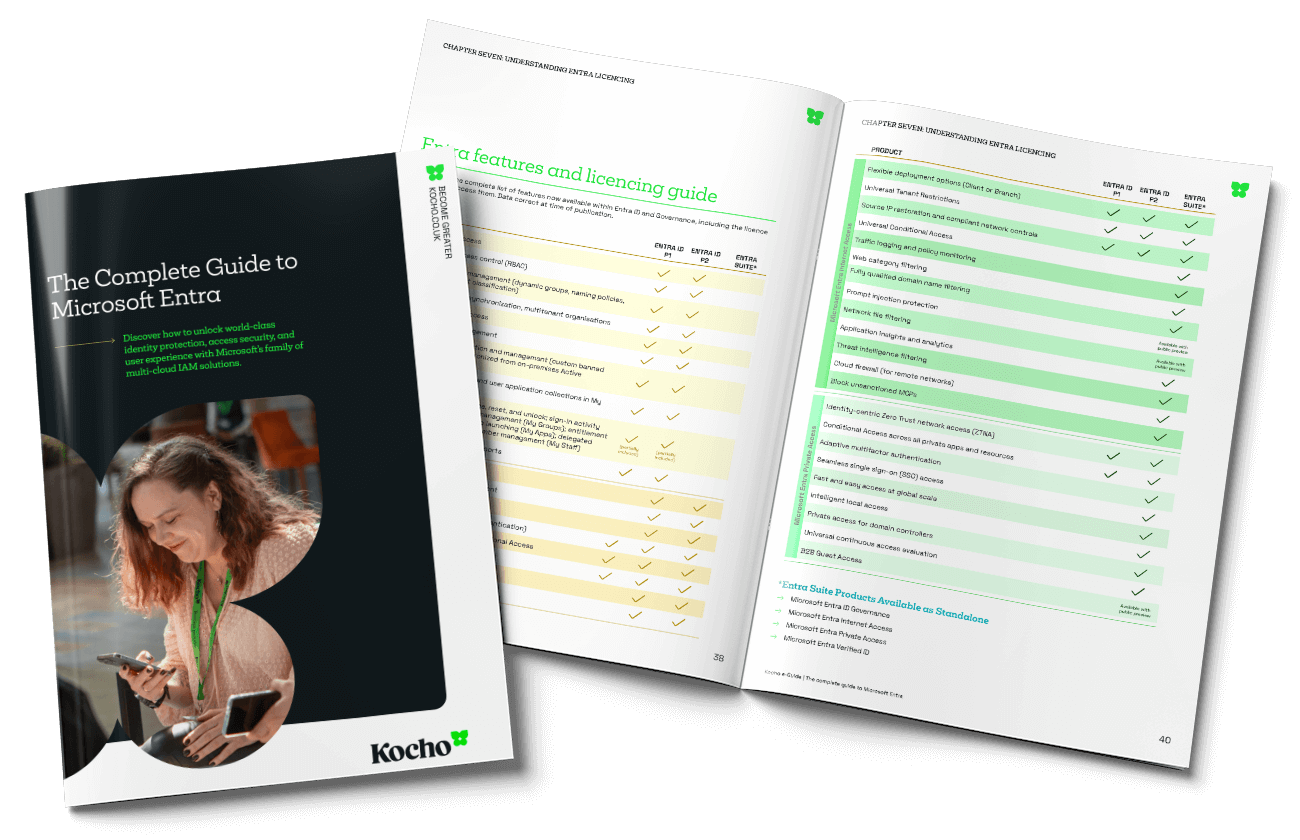
Microsoft Entra brings identity, access, governance, and security together in a single platform, supporting modern IAM across cloud, hybrid, and regulated environments.
But Entra only delivers value when its capabilities are deliberately designed and operated together. Architecture, policy, and lifecycle discipline determine whether it functions as a platform or fragments into features.
Kocho was built as an identity‑first Microsoft partner. We understand Microsoft Entra in depth and apply its full capability deliberately, designing IAM architectures that work end to end. The result is an identity platform that is coherent, operable, and resilient, not just implemented..

Case studies
Who we've helped
Talk to the original identity-centric Microsoft partner
When identity becomes critical to security or transformation, organisations turn to Kocho. We deliver Microsoft‑first IAM programmes built on Microsoft Entra, designed to scale securely across cloud, hybrid, and regulated environments.
Our focus is simple. Reduce complexity. Strengthen control. Build identity foundations that last.
Talk to our team today.
Frequently asked questions about IAM
-
Identity and access management (IAM) controls who or what can access systems, applications, and data, under what conditions, and with what level of trust. It underpins security, compliance, and modern digital operations.
-
Most modern attacks target credentials and access paths rather than infrastructure. As organisations adopt cloud services, SaaS, AI, and automation, identity has become the primary control point for enforcing security.
-
Legacy directories, custom scripts, and ageing identity platforms introduce complexity, reduce visibility, and make access harder to govern. Over time, this increases security risk and operational overhead.
-
No. While IAM is implemented by IT and security teams, it directly affects productivity, risk management, compliance, and user experience across the organisation. Poor IAM impacts far more than technology.
-
No. Effective IAM is delivered through a phased roadmap. Capabilities are introduced in sequence, aligned to organisational maturity, risk, and priorities rather than deployed as a single transformation.
-
IAM enforces Zero Trust principles by verifying identity continuously, applying least‑privilege access, and assessing risk at sign‑in and during sessions. Identity is the enforcement layer for Zero Trust strategies.
-
IAM includes external identities such as partners, contractors, and customers. External identity management ensures secure, scalable access without exposing internal systems or weakening governance.
-
Well‑executed IAM delivers consistent access control, stronger security, reduced reliance on legacy tooling, clearer governance, and a scalable foundation for future change.
-
Microsoft‑first partners design identity architectures that fully align with Microsoft Entra. This reduces complexity, avoids duplicated tooling, and ensures IAM programmes are operable, secure, and sustainable long term.


























A clear pathway
Book your Entra ID Discovery & Roadmapping Workshop
Understand how to achieve more efficient, secure, and cost-effective identity and access management.
This is your opportunity to:
- Understand the gaps and challenges costing your organisation time and money.
- Gain a strategy that aligns identity management with your long-term business goals.
- Design an affordable solution that mitigates security risks and improves user experiences.