Authentication has strengthened, yet many serious breaches now occur during operational trust decisions. This article explores how Microsoft Entra Verified ID and Face Check bring structured assurance to service desk verification.
Over the last few years, organisations have made genuine progress improving login security within access management strategies. Multi-factor authentication (MFA) is now commonplace, passwordless adoption is growing, and conditional access policies have become considerably more sophisticated.
But as authentication has strengthened, attackers have adapted. Rather than attempting to defeat sign-in controls, they increasingly target the operational processes that surround identity, and the service desk in particular.
This is not to diminish the critical importance of phishing-resistant authentication. It remains foundational. The point is simply that mature identity security cannot stop there.
Risk continues well beyond login, and strategy needs to reflect that.
How attackers target service desk identity processes
Groups like Scattered Spider have demonstrated how effective identity-focused attacks can be without relying on zero-day exploits or sophisticated malware.
Their approach targets people and processes, exploiting trust rather than technology. They impersonate employees, target support teams and use internal terminology convincingly enough to gain confidence quickly. They understand how organisations work, how requests flow and where authority sits.
Exploiting familiarity and weaponising urgency.
Once access is granted, they operate using legitimate tools and administrative channels, blending into normal activity.
And, as we’ve seen in some major high-profile incidents in recent times, this can quickly escalate and have significant repercussions, affecting operational resilience, regulatory exposure and organisational trust.
AI-enabled impersonation has changed identity trust signals
Of course, this has all been brought into sharper focus through the extraordinary advances in artificial intelligence (AI).
Deepfake voice and video technology challenge long-standing assumptions about familiarity and authenticity. Signals that once reinforced confidence are becoming easier to replicate.
Knowledge-based questions and human judgement alone were never designed to handle realistic synthetic impersonation.
Service desk teams are therefore operating in an environment where:
- Attackers sound more convincing
- Contextual knowledge is easier to obtain
- Pressure to resolve requests remains high
Traditional verification models built on conversational trust, security questions and device assumptions were adequate for a simpler threat model. Today, they create dangerous inconsistency.
Different agents make different decisions under similar conditions. Urgent requests receive different scrutiny depending on experience and workload.
The process becomes subjective, and from a security perspective, subjectivity creates risk.

latest edition
Everything you need to know about Microsoft Entra
A clear, practical view of how Microsoft Entra works as a unified platform.
Expert guidance on modern identity design, security, governance, and Entra licensing.
Discover how you can:
- Run Entra as one coherent identity platform
- Apply end-to-end security and governance
- Modernise IAM safely, from MIM to AI-driven identity
Moving from identity authorisation to identity assurance
Organisations are now faced with the challenge of verifying identities in a world where traditional trust signals have been undermined.
To put it another way: identity can no longer be taken at face value. It has to be verified with confidence before high-risk decisions are made.
This is the distinction between identity authorisation and identity assurance. Authorisation asks whether credentials check out. Assurance asks whether there is measurable confidence that the right person is behind the request, at the moment the decision is being made.
Introducing identity assurance means embedding a structured verification step at the precise moment a sensitive decision is initiated. Instead of leaving agents to judge credibility in real time, the workflow provides an objective signal that either supports or challenges the request before any action proceeds.
Human judgement remains central. Context, nuance and operational experience still matter, especially when requests don’t fit neat technical rules. The difference is that judgement is now supported by consistent, repeatable evidence, making decisions more reliable, defensible and resilient under pressure.
Microsoft Entra Verified ID and Face Check for service desk identity assurance
This is reflected in the evolution of Microsoft Entra, in particular in its development of Entra Verified ID and Face Check.
Verified ID provides a consistent mechanism for issuing and verifying credentials using decentralised identity principles.
It supports onboarding workflows, access decisions and service desk validation without requiring custom integrations at every step. Recent platform improvements allow identity verification partners to be onboarded directly through the Entra portal and Security Store, including government ID checks and higher-assurance account recovery flows.
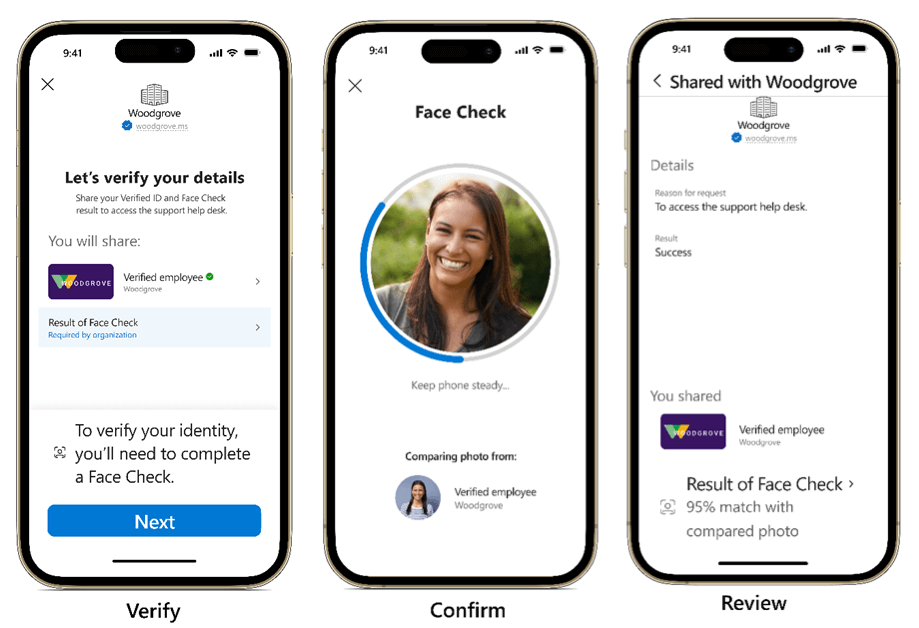
Face Check adds a further assurance layer by comparing a live selfie against a trusted corporate profile photo held in the organisation’s identity system.
Users complete live verification through Microsoft Authenticator, where a real-time image is compared against the verified profile photo. The outcome is an assurance score rather than biometric data itself. Support teams receive a confidence signal that informs the decision, without handling or viewing underlying biometric information.
That change shifts how support teams operate. Instead of relying only on familiarity or instinct, they have consistent, repeatable evidence that becomes part of the workflow itself.
Organisations can then:
There is a caveat here of which organisations need to be aware.
When a Verified ID is issued, Microsoft Authenticator retrieves the organisation’s approved profile photo, or configured external data source, and binds it to the credential. Face Check then compares the live image against that reference.
This becomes a problem if the employee has uploaded an avatar, a photo of their dog, or their favourite football club’s badge. To address this, Verified ID can be pointed towards an external data source to ensure a more corporate-appropriate image is used.
This places greater emphasis on organisations treating profile photos as identity data rather than cosmetic preference. That means governing with the same rigour as any other identity attribute and maintaining it as part of the identity lifecycle.
Get that right, and Face Check becomes a genuinely powerful verification tool.
Bringing identity assurance into service workflows
Most organisations already rely on IT service management platforms such as ServiceNow to manage support activity.
Identity assurance strengthens these workflows without replacing them.
A high-risk request is initiated. Verification is triggered automatically. The user receives a secure verification link or QR code. Live verification is completed through Microsoft Authenticator. An assurance score returns to the workflow. The request proceeds only if policy thresholds are met.
It keeps process friction to a minimum while enabling consistent, evidence-based decision-making under pressure.
Trust should work both ways in identity verification
It’s also worth remembering that impersonation risk doesn’t only flow one way.
Attackers can also impersonate service desk staff, contacting users directly and attempting to persuade them to take unsafe actions, or give them remote access to their devices. We should therefore consider how identity assurance enables reverse verification. In other words, allowing users to validate a support agent’s identity before proceeding with sensitive activity.
The same mechanism that protects the service desk from impersonation protects the user from it too.
This bi-directional trust is an important evolution. Identity workflows that only verify in one direction leave half the attack surface unaddressed.
Account recovery is where assurance matters most
Account recovery scenarios are often the highest-risk moments in identity operations.
Users may have lost devices or credentials, leaving service desks under pressure to restore access quickly. Historically, this often resulted in manual escalation or exceptions.
Identity assurance allows recovery workflows to include structured validation, including verification of government issued ID through approved identity partners in a privacy-centric way, and live checks before temporary access is granted.
Recovery becomes policy-driven rather than discretionary.
The real question for identity maturity
Robust, phishing-resistant authentication remains essential and without it estates are vulnerable.
But mature identity strategies increasingly recognise that risk doesn’t end when a user signs in. It continues through every decision an organisation makes as access changes, privilege escalates and accounts are recovered.
Organisations that treat identity assurance as a natural extension of their identity programme, rather than a future consideration, will be significantly better positioned to resist the next generation of impersonation-driven attacks.
Those that continue to treat service desk verification as an IT process, rather than a security control, are leaving one of their most consequential decision points largely undefended.
FAQs: Identity assurance, service desk risk, and Face Check
-
Modern authentication controls are stronger than ever. As a result, attackers increasingly target the operational decisions that follow login, particularly password resets, privilege changes and account recovery requests handled by service desks. These workflows often require rapid trust decisions under pressure, creating an attractive entry point for impersonation and social engineering attacks.
-
Identity assurance introduces a structured verification step into high-risk service workflows. Instead of relying solely on knowledge-based questions or conversational judgement, the process produces a defined confidence signal before sensitive actions proceed. This makes decisions more consistent and defensible.
-
Microsoft Entra Verified ID allows organisations to issue verifiable credentials that are bound to trusted identity attributes, including a governed corporate profile image. When verification is triggered, Microsoft Authenticator retrieves that approved image and compares it with a live selfie through Face Check.
The outcome is an assurance score that is returned to the service workflow. Support teams receive a confidence signal rather than biometric data, enabling policy-driven decisions without handling underlying facial images.
-
No. The service desk receives only an assurance score indicating the level of confidence in the match. The underlying image comparison is processed transiently, and support teams do not access or store facial biometric data.
-
Face Check compares a live selfie against the corporate profile image associated with a Verified ID credential. If that image is inaccurate, outdated or replaced with a non-compliant photo, assurance quality is reduced. Organisations should treat profile photos as governed identity data, maintained as part of the identity lifecycle.
-
Account recovery is often one of the highest-risk identity moments. Identity assurance allows recovery workflows to include structured validation, including live verification and, where required, government-issued ID checks through approved identity partners. Recovery decisions become policy-driven rather than discretionary.
-
Yes. Identity assurance can support reverse verification, allowing users to validate the identity of a support agent before proceeding with sensitive actions. This creates bi-directional trust and reduces impersonation risk on both sides of the interaction.
-
No. Human judgement remains central. Identity assurance strengthens it by providing consistent evidence to support decisions made under operational pressure.

Secure Service Desk with Entra
Risk has moved beyond authentication
Attackers are targeting recovery flows, manipulating helpdesks, and exploiting outdated verification.
See how Microsoft Verified ID, Face Check and real-time identity assurance close the gaps traditional IAM leaves exposed.
Strengthen privileged access, automate secure recovery, and verify people, not just credentials.
If you liked this, please share on your social channels. Or, if you want to find out how Verified ID and Face Check fit into Microsoft Entra’s unified identity platform, download the latest version of our Complete Guide to Entra here.

Great emails start here
Sign up for free resources and exclusive invites
Subscribe to the Kocho mailing list if you want:
- Demos of the latest Microsoft tech
- Invites to exclusive events and webinars
- Resources that make your job easier

Don't Miss
Great security & compliance resources

Don't Miss
Great enterprise identity resources
























Got a question? Need more information?
Our expert team is here to help.