












Access security designed around real‑world risk
In modern organisations, work happens everywhere. Across hybrid environments, SaaS platforms, remote teams, partner ecosystems, and increasingly AI-driven services.
Secure access management defines how employees, contractors, and partners prove who they are, what they can access, and whether that access should continue. It can no longer rely on static trust assumptions or legacy network boundaries.
Access must adapt to risk in real time, enforcing control without interrupting productivity.
As an original Microsoft identity-first partner, Kocho designs secure access management solutions that satisfy security teams and feel invisible to users.
Why secure access management breaks down in modern estates
As digital estates expand, access control often evolves reactively. The result is inconsistent enforcement, persistent credential risk, and access architectures that work against the people using them.
Sign-in decisions aren’t enough
Modern access risk continues after login. Session behaviour, device state and context change, and most architectures can’t respond.
Inconsistent app access creates gaps
Cloud and legacy apps rarely share authentication standards. This creates uneven enforcement: strong in some areas, weak in others.
Outdated authentication methods create exposure
Password-based access remains widespread despite known risks. Without phishing-resistant methods, credential abuse remains a reliable attack vector.
Friction drives user to find workarounds
When security creates unnecessary friction, it can create frustration and invite users to find ways around it, undermining the protection it was meant to provide.
Access that responds to risk rather than assumptions
In well-governed identity environments, access decisions respond to real-world context, not fixed rules or network assumptions.
That means evaluating risk continuously, not just at the moment someone signs in.
Secure access management defines how:
- Sign-in decisions are actively verified, not assumed
- Device health and user risk shape access in real time
- Conditional access follows architecture, not reactive habit
- Password dependency gives way to phishing-resistant authentication
- Access stays consistent across SaaS and legacy applications
- Risk is evaluated continuously, not just at the door
Security that works for users, not against them
When security feels cumbersome it creates frustration and impacts productivity. Getting the balance right, where security feels invisible is what we do.
Secure access management design should:
- Strengthen authentication without increasing complexity
- Replace passwords with passwordless and phishing-resistant alternatives
- Align access decisions to user role and real-time risk
- Deliver a consistent experience across every application
- Eliminate unnecessary prompts without compromising enforcement
Kocho designs secure access management architectures that give security teams the control they need and users the simplicity they expect.
Well-designed access management changes how people work
When secure access management adapts to risk and supports how people actually work, the benefits are immediate.
Organisations see:
- Lower account compromise risk
- Stronger resistance to phishing and credential abuse
- Consistent, enforceable policy across applications
- Reduced prompt fatigue and password reliance
- Greater visibility into workforce access behaviour
- Fewer access delays and higher productivity
Access becomes a business enabler rather than a compliance overhead.
The thing that stands out about Kocho is their level of professionalism and the experience they have in identity and access management. They are market leaders and that really shows.
Stuart Purkiss-Webb
Infrastructure Architect, Aviva
The controls that make secure access management work
Secure access management is not a single control. It is an architecture of disciplines that work together to enforce consistent, risk-aware access across your full identity estate. Kocho delivers across all of them.
Conditional access strategy and architecture
Designing risk-based policies that respond to identity, device, and location signals, structured to be enforceable and aligned to business risk.
Secure access for hybrid and remote work
Access that adapts to context and user risk rather than network location. Consistent security wherever your people work.
Passwordless and phishing-resistant access
Stronger identity assurance through MFA and phishing-resistant credentials, reducing sign-in friction while cutting exposure to credential-based attacks.
Consistent access across cloud and legacy applications
Unified authentication and enforcement across the full application estate, closing the gaps that fragmented access control creates across your environment.
Frictionless user experience and adoption
Access controls designed around how people work reduces frustration and unnecessary delays, while boosting efficiency and productivity.
Continuous access evaluation and session risk
Real-time risk signals that extend enforcement beyond sign-in, revoking or stepping up access as conditions change throughout the session.
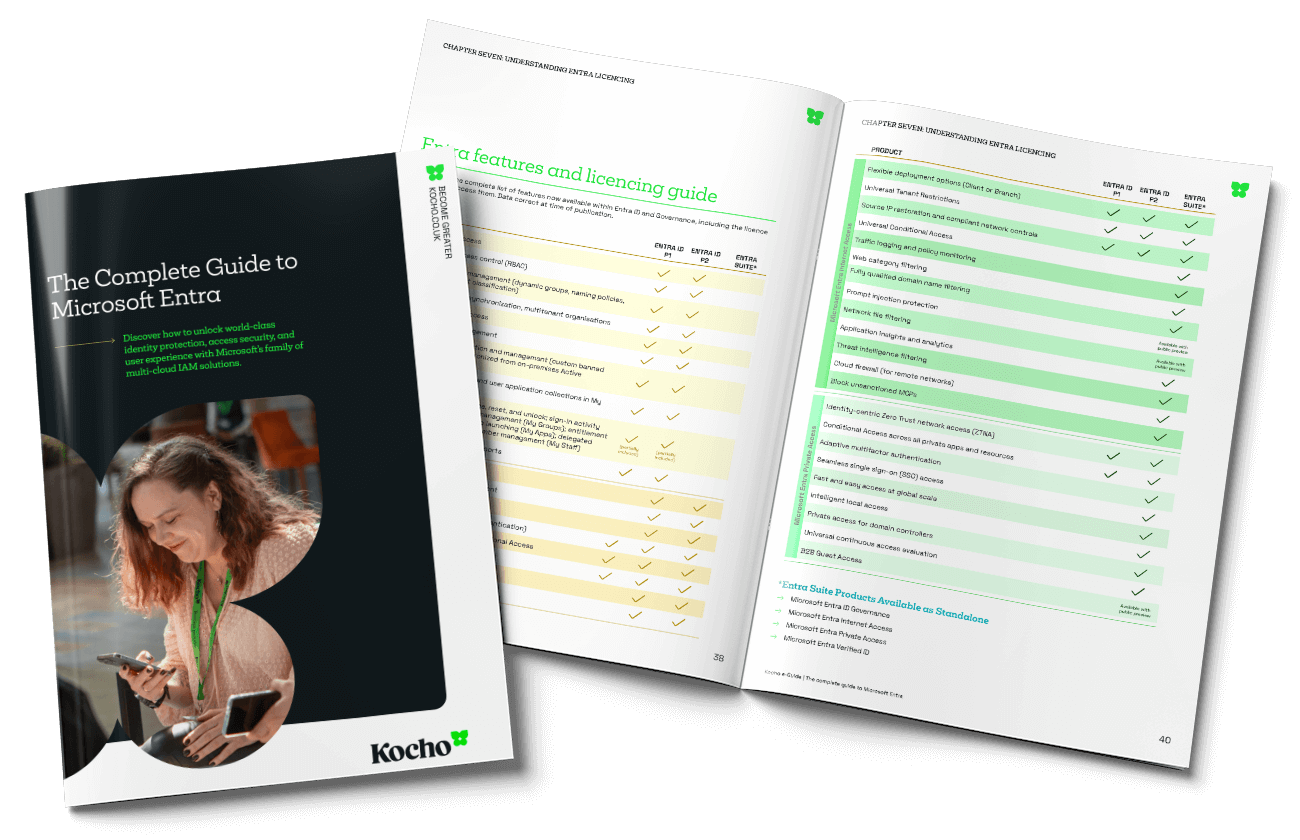
Our Microsoft Entra expertise turns secure access into strategic advantage
Kocho is the original Microsoft identity-first partner. That depth of specialism means we understand Microsoft Entra’s capabilities better than anyone, and we know how to unlock them in ways that translate directly into stronger, more resilient secure access management for your organisation.
We design the policies, implement the authentication standards, and build the enforcement frameworks that turn Microsoft Entra’s capability into secure, scalable access management that works for security teams and users alike.
The outcome is coherent, resilient access that holds up as your organisation grows.

Case studies
Who we've helped
Let’s talk about your access architecture
Whether you’re dealing with authentication friction, legacy design decisions or unclear enforcement, the right conversation often comes before the right solution.
Speak to our identity specialists about what’s working, what isn’t and how to move forward.
Frequently asked questions about secure workforce access
-
Secure access management governs how employees and contractors authenticate and gain access to systems. It ensures that access decisions are continuously evaluated against contextual risk and organisational policy, adapting in real time rather than relying on static trust assumptions.
-
By applying identity-centred enforcement rather than network-based trust, organisations can adapt access decisions dynamically to context and risk. This means evaluating who is signing in, from what device, under what risk conditions, regardless of where they are connecting from.
-
Yes. Effective secure access management must integrate cloud and legacy systems into a consistent authentication and enforcement model. Without this, policy gaps appear at the boundaries between modern and legacy environments, creating exploitable inconsistencies in access control.
-
Secure access management is one of the foundational pillars of a Zero Trust architecture. Zero Trust requires that no user or device is trusted by default, and that access is continuously verified against risk signals. Access controls including conditional access, phishing-resistant authentication, and session risk evaluation are the practical mechanisms through which Zero Trust principles are enforced.
-
Microsoft Entra provides the identity platform underpinning modern secure access management. Its capabilities include conditional access policy enforcement, phishing-resistant authentication methods, identity risk detection, and continuous access evaluation. Together these enable organisations to build adaptive, risk-aware access controls across their full application estate.
-
Continuous access evaluation extends enforcement beyond the point of sign-in, monitoring risk signals throughout an active session. If a user’s risk profile changes, their device becomes non-compliant, or a threat is detected, access can be revoked or stepped up in real time rather than waiting for the next authentication event.
-
The most effective starting point is an assessment of the current access architecture: existing risk-based access policies, authentication methods in use, application coverage, and gaps in enforcement. From there, a structured remediation roadmap can prioritise the changes that reduce the most risk with the least disruption to users. Kocho provides this assessment as part of its secure workforce access advisory service.


























A clear pathway
Book your Entra ID Discovery & Roadmapping Workshop
Understand how to achieve more efficient, secure, and cost-effective identity and access management.
This is your opportunity to:
- Understand the gaps and challenges costing your organisation time and money.
- Gain a strategy that aligns identity management with your long-term business goals.
- Design an affordable solution that mitigates security risks and improves user experiences.